OK, so we know that to secure and control our network, we need full visibility into the traffic passing through it. What we would like to have, is a truly non-intrusive device that will offer that visibility, without affecting the network. There are several approaches to deploying such a device in an out-of-band fashion. Two of the most common ones are either connecting the device to a test access point (tap) or to a Switch Port Analyzer (SPAN).
Neither of the approaches will affect the real network traffic, and in either of the approaches the out-of-band appliances can be connected and disconnected from the network without any downtime or disruption. Also, if the monitoring device should, for whatever reason, fail (such as due to a power outage or software malfunction), the traffic will nevertheless continue to flow through the network as usual.
Most network engineers will agree, that of the various options for carrying this out, one of the best – both as a traditional method and as a verifiable and future-ready one – is the classic network tap.
Network taps, a purpose-built piece of hardware whose only function is to copy network data and send it to any and all devices connected to it, will provide the optimum starting point for network visibility. Not only do they replicate all of the network data that flows through them (yes – you heard right: 100%!), they can be strategically placed throughout the network to enable visibility into the network traffic full stack of OSI layers.
Active vs. Passive taps – what’s the difference?
Taps come in two basic categories: active and passive – and although there are additional differences, they can best be described as follows:
- An active tap is the chip or electronic element that enables the data to flow through it, and it then duplicates and passes that data along to an endpoint such as an inspection or analysis device. It can work in either copper or fibre-cabling environments. It needs to be powered at all times. In the event of a power outage, these taps may have battery backup to keep them up-and-running and will send an alert notification to flag the new status. A bypass tap is a special type of active tap that contains a relay switch that closes with loss of power, preserving the network connection and reducing traffic interruption - though in case of power loss the traffic to the monitoring device will cease.
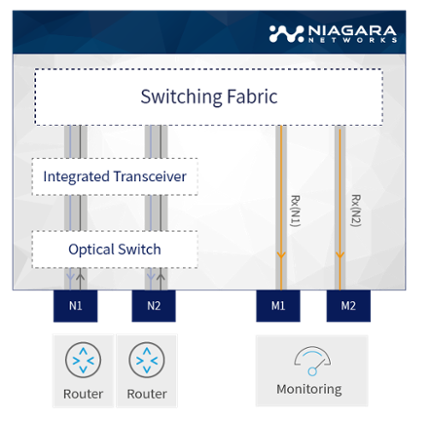 This figure depicts an active tap configured to split mode, where each network direction is copied to a separate monitoring interface M1 and M2. Some active taps may also be configured to aggregate mode where both network directions are copied to a single monitoring port output.
This figure depicts an active tap configured to split mode, where each network direction is copied to a separate monitoring interface M1 and M2. Some active taps may also be configured to aggregate mode where both network directions are copied to a single monitoring port output.
- A passive optical tap is a tool that splits the light (the data traffic) passing through a fibre cable. It enables the data to flow through it, while at the same time, splitting that light, thus seamlessly duplicating and passing it along to an endpoint such as an inspection or analysis device. Depending on the loss budget you can select the split ratio, i.e how much light is going to the monitoring appliance and how much goes to the network. It has no need for any power source.
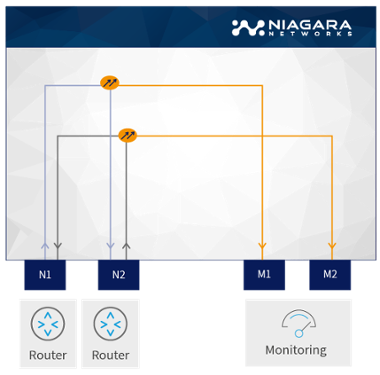 This figure depicts passive tap configuration. A coupler/splitter (marked in orange) is responsible for 'splitting' the light. The user can specify the split ration between light (in dB) continuing on the network and that going to the monitor port depending on loss budget of the deployment.
This figure depicts passive tap configuration. A coupler/splitter (marked in orange) is responsible for 'splitting' the light. The user can specify the split ration between light (in dB) continuing on the network and that going to the monitor port depending on loss budget of the deployment.
Active taps actively manage the traffic using switch-like mechanisms, and are thus able to offer additional useful functionality such as aggregation and traffic injection. In aggregation both sides of a full duplex communication are sent to a single monitoring port. In traffic injection, we enable the monitoring appliance to inject traffic to the network. Examples of traffic injection can be ‘TCP Reset’ or ‘ICMP not available’ notifications.
Taps are truly non-intrusive and seamless. They provide clear, 100% network traffic visibility into each packet of data (at full bandwidth), without overloading the network resources or using up the processing capabilities of your switches. They also do not require configuration or programming time from your network designers – freeing up this valuable human resource as well.
Deployment
When deploying network taps, it is essential to match them to the network’s physical characteristics and behavior, taking into account network speed capabilities and cabling types. For example, If the network cabling is made up of copper in a 1 Gigabit network, it will need to use an active network tap (as previously explained, passive network taps will not work in environments made up of copper cabling – only fibre).
Network architects can use both passive and active network taps in fiber environments, but there are different requirements for single and multimode implementations. Network taps are built for specific 1Gb, 10Gb, 40Gb, and 100Gb environments to ensure that throughput to the connected device matches the rate at which data is flowing through the network. It is essential, therefore, to match the taps with the devices’ capabilities.
In addition to just copying and sending traffic data, network taps combine additional functionality for more efficiently supporting security and performance optimization. As such, a company’s network designers and implementers should take into consideration the placing of the network taps at such points within the network, where the most important core business operations of the enterprise take place.
The network tapping results in an accumulation or clustering of data, generally referred to as traffic aggregation. Network designers need to know what to do with the traffic – in other words, how to manage that data:
- How to look at the data
- What to look for in the data
- Where to send that data
The answer lies with – next up – network packet brokers (NPBs).
Network taps and network packet brokers (NPBs)
Another aspect of network visibility, deals with the traffic data that is aggregated from the network taps. Typically, the taps are coupled with network packet brokers (NPBs). Like the taps, packet brokers are hardware devices. They are designed to provide the right traffic to the right tool connected to it.
The coupling of the two (NPBs and taps), provide an additional, more sophisticated, level of functionality that will ensure enhanced visibility across all the devices that are connected throughout the network. When the packet broker is placed between the network tap and the intended security or monitoring solutions, it can route the traffic in an intelligent manner, by using different port mapping schemes.
The combination of network taps and packet brokers, enables network architects to design a complete connectivity solution that includes the ability to regenerate, aggregate, filter, and load balance data. This ensures that each and every element in a network monitoring, security, and performance optimization schema has maximum and optimum visibility to carry out its multiple functions and tasks in the most efficient manner.
As a bonus, every packet broker can itself also act as an active tap, since it contains built-in tap functionality and can ‘act’ as an active and passive tap as needed. This can be an alternative to just adding random taps to network points.
Guaranteed data capture
There are many ways to copy traffic. Usually SPAN and copy ports are used with switches. These are not guaranteed because although considered non-intrusive, a SPAN port has an effect on the monitored traffic by changing the timing of the frame interaction. If the switch or router becomes overloaded, it may cause the SPAN port to drop frames. The reason for that is, that the primary focus of the device’s spanning algorithm is switching or routing. The switch will always treat the SPAN data with a lower priority than normal traffic. Therefore, if replicating a frame becomes an issue, spanning will be suspended. Active taps, on the other hand, offer guaranteed data capture because they always copy the traffic regardless of external events.
As explained, taps provide 100% traffic data capture. Beginning May of 2018, enterprises in Europe must guarantee complete and consistent data integrity over the networks – according to the new European GDPR (General Data Protection Regulation) guidelines. Where most other traffic SPAN/mirroring and capture mechanisms may drop packets or lose data due to network availability (and other) issues – tap technology virtually guarantees that GDPR requirements can be met.
Summary
Consistent, dependable access to 100 percent of the network traffic is the key feature of active and passive taps. Combined with network packet brokers, taps represent a very attractive solution for network visibility.
Niagara Networks provides taps for both active and passive traffic flow, depending on specific use cases, enabling network architects to design a complete connectivity solution that includes the ability to regenerate, aggregate, filter, and load balance data.
Need help choosing the right Network Tap? Talk to our network visibility experts today.
 By: Yigal Amram
By: Yigal Amram