Many organizations operate smaller on-premises environments such as small data centers, branch locations, campus networks, and industrial sites. While these environments may not have the scale of large hyperscale data centers, they still require reliable network monitoring and cybersecurity visibility.
- Check out our latest Blogs
-
Products
Our Products
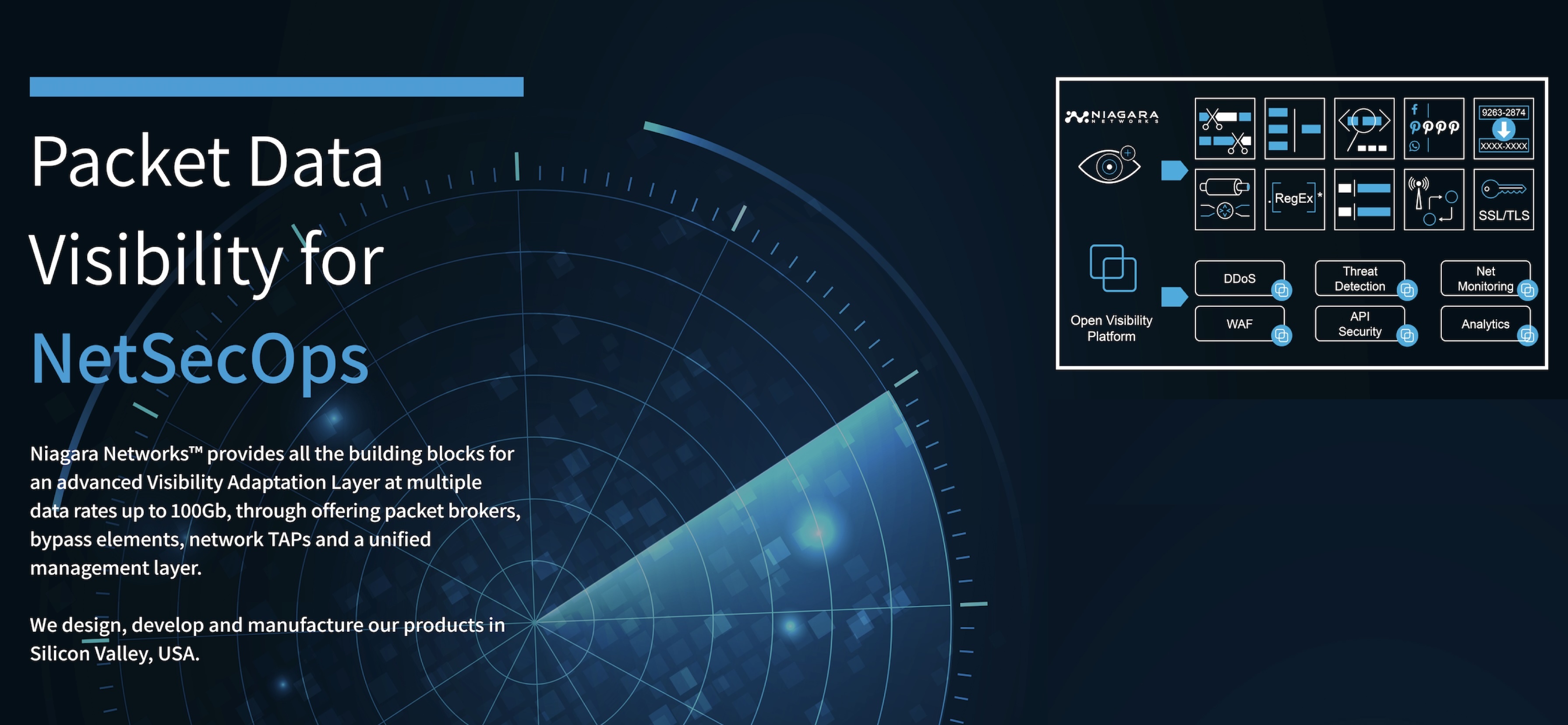
We Design, Develop and Manufacture our Products in Silicon Valley, USA.
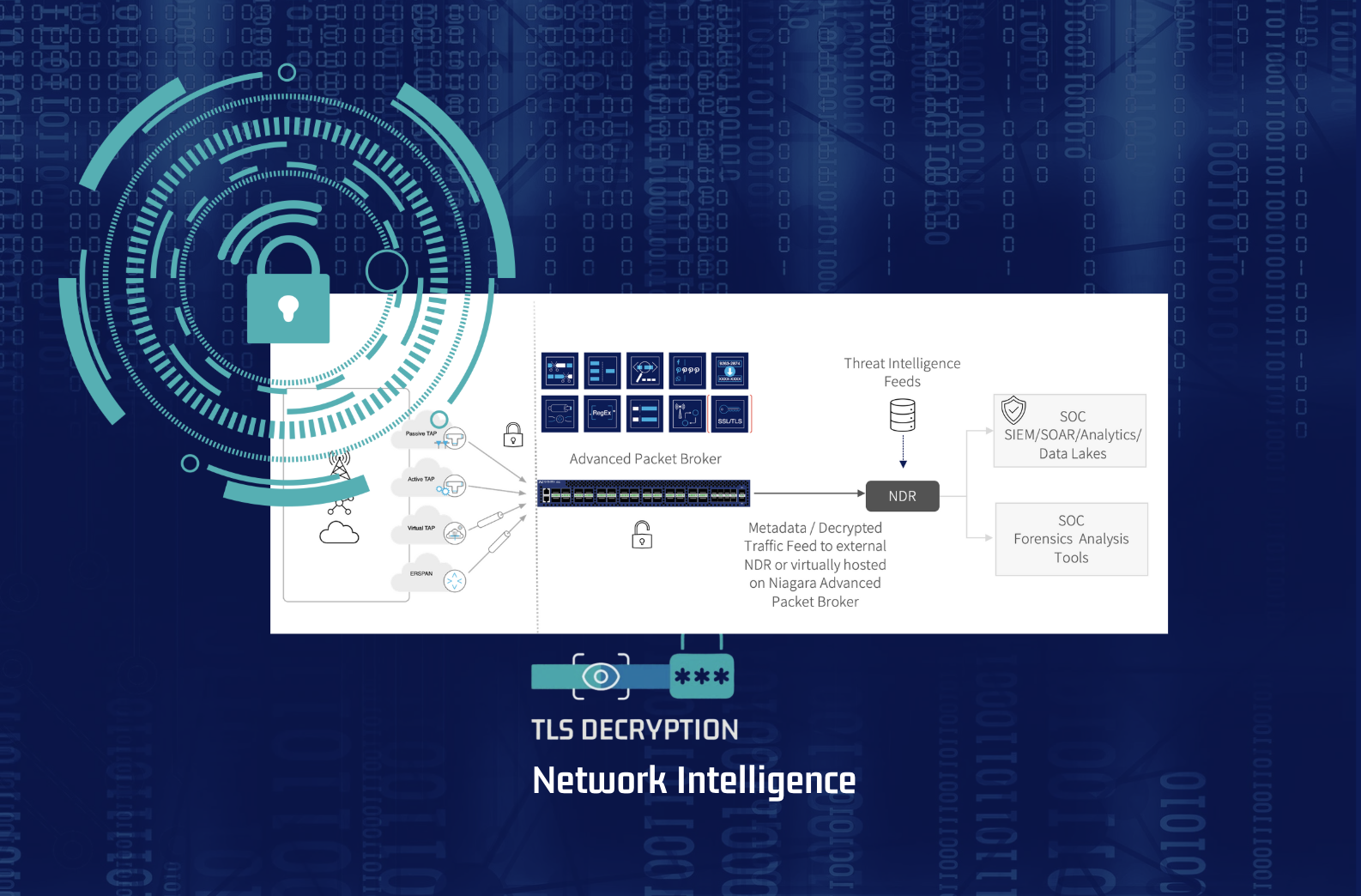
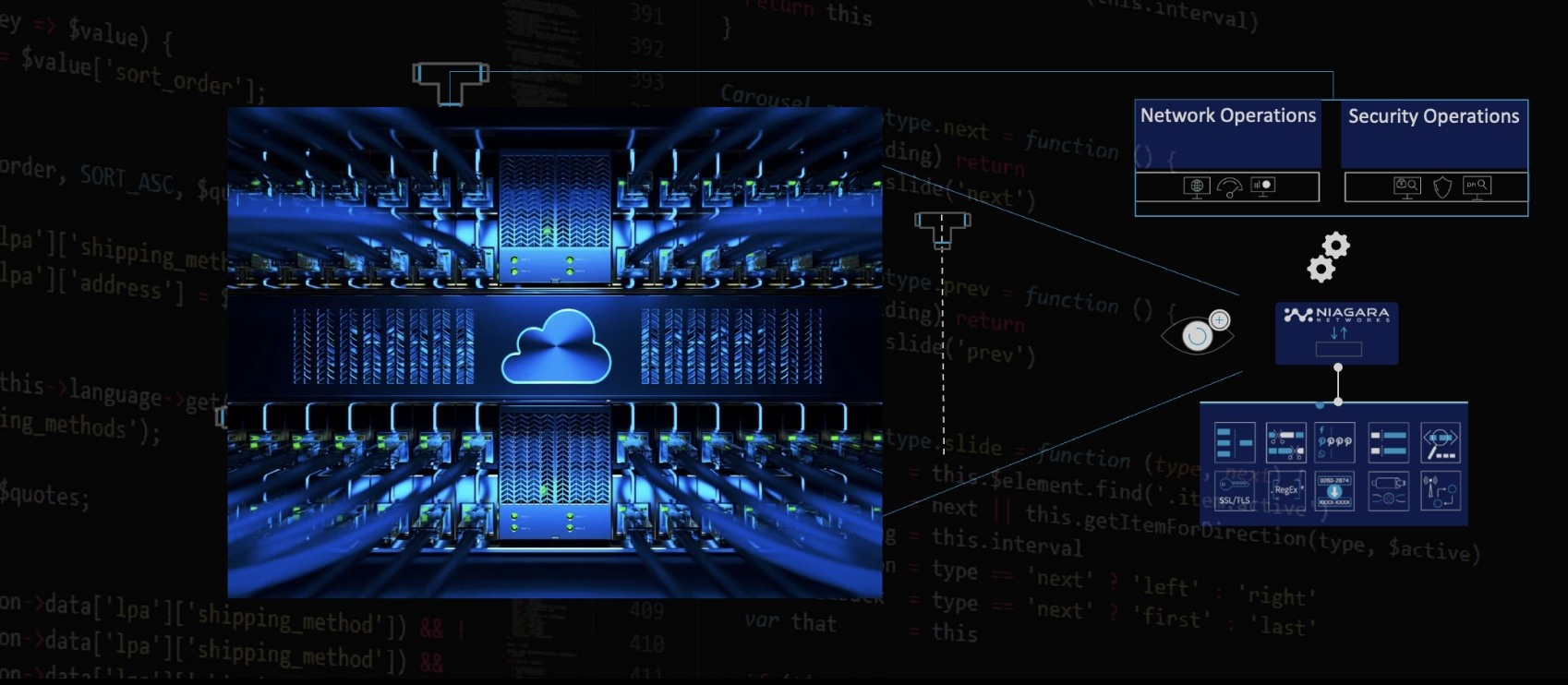
Niagara Networks™ delivers all the essential building blocks for high-performance visibility across physical and virtual network infrastructures. Our comprehensive portfolio includes Network Packet Brokers, Bypass Switches, Network TAPs, and a unified orchestration layer for seamless visibility and control.
Network Visibility Platforms – MADE in the USACloud VisibilityData Center VisibilityAdvanced Network Packet Brokers
Network Packet Broker Aggregators
Traffic IntelligenceHigh-Availability & TAPsVisibility OrchestrationOpen Visibility -
Solutions
Our Solutions
Niagara Networks™ solutions enable NetOps and SecOps teams easily and efficiently operate and administer multiple security platforms and service scale, while reducing operational expenses and downtime.
Network Visibility Solutions for Virtual and Physical InfrastructureIndustries We ServeNetwork Issues that we SolveNetwork SecurityNetwork Traffic AccessInline Bypass & High-Availability FailoverMobile Subscriber-Aware VisibilitySolution for Hybrid Cloud ObservabilityCompetitive -
Partners
Our Partners
Niagara Networks™ partners with world-class technology leaders to provide high performance network visibility and security.
Our partners include companies that are part of our technology alliance and companies who take part in distributing Niagara's solutions.
Our Alliance of Technology Innovators & Channels-
Channel Partners
Expanding reach and value through a strong
worldwide network of channel partners -
Technology Alliance
Empowering innovation through strategic
alliances with leading technology providers
-
Channel Partners
- Resources
- Support
- Company
- Contact Us
-