Quantum computing has the potential to revolutionize many fields, including encryption.
In recent years, there has been a lot of interest in using quantum computers to break traditional encryption methods, which could have major implications for the security of sensitive data.
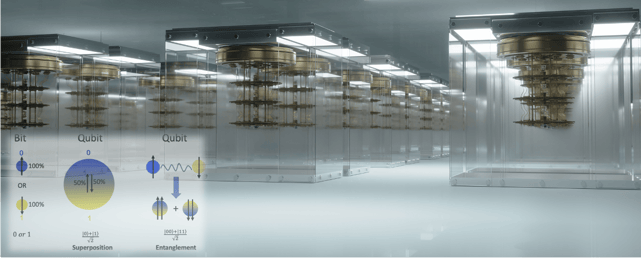
Quantum Computing surpasses traditional binary computer limitations and allows a significant improvement in memory and calculation power, and is an effective solution to computational problems, using a computer architecture based on quantum theory.
The central principles of quantum theory are reflected in quantum computer architecture via superposition and entanglement in quantum mechanics to enable advanced calculations. Superposition allows a quantum system to exist in multiple states at once, allowing it to perform multiple calculations simultaneously. Entanglement occurs when two or more particles become correlated, linking their properties even when separated by large distances. This allows for the instant transfer of information between the particles, enabling calculations that classical computers cannot perform. For those that are curious and interested to learn the internals of quantum computing architecture, feel free to dive into the following academic article >>
Getting back to the impact on cryptography, the world of cryptography relies on solving complicated mathematical problems as a basis for performing security operations such as encrypting information or performing digital signatures. The latest advances in quantum computing may pose a real threat to organizations that use existing algorithms/protocols that are not immune to this type of computing. Furthermore, sensitive information is already being collected today in preparation for the time when it can be hacked and deciphered, and therefore organizations around the world are demanding an improvement in information protection capabilities to avoid potential security and privacy breaches in the future.
To clearly understand the threats and vulnerabilities, hereunder are a few examples:
- Organizations that use a public-private key infrastructure (PKI), which relies on protection using algorithms such as RSA or ECC, may be exposed to sender spoofing attacks or decryption of encrypted content.
- Quantum computing may allow information confidentiality to be compromised when working with the Diffie-Hellman protocol, which is used to share keys over an insecure network.
- The use of quantum computing also reveals vulnerabilities of the DSA algorithm, which is used in digital signature processes and in checking its integrity, which may allow a potential attacker to forge a sender.
- Quantum computing capabilities might drive "unfair" mining of cryptocurrency. An attacker may mine a cryptocurrency with an ability that is clearly superior to peers without quantum computing capability, thus maliciously tipping the scales in his favor. In more radical cases, attackers might even hack blockchain and modify existing records without exposing the change or even create an unplanned branching in an existing chain, defined as a “new fork”. As a result, this may affect the validity/acceptability of digital contracts and other services that rely on blockchain technology. If we stay at the WEB 3.0 framework, an attacker may produce a non-fungible token (NFT) for a fake digital asset (such as a fake digital artwork), identical to the one that exists for an authentic digital asset. Such a hack might allow the creation of a false representation to buyers that they have an authentic digital asset.
- Possibility of shortening the time for cracking AES encryption, considering that the number of steps required to perform the cracking on the traditional computer is 2∧ 128 , while that the number of steps required in a quantum computer is reduced to 2∧64. It should be noted that in the case of AES, the use of a longer key (such as AES 256 bit in GCM mode) may in some cases provide an adequate security response in terms of cost versus benefit for the near future.
- A quantum computer will also be able to mine virtual currencies at a fast rate compared to the mining rate of a traditional computer, while cracking the 256-SHA algorithm (2∧ 128 vs. 2∧ 256), thus potentially being able to topple the virtual currency market and market shares which are trusted by them.
- The world of quantum computing is taking the first steps today to break one-way hashing functions by quantum simulators that enable finding a local minimum for a function (mathematical solution for a function) in fast runtime. To illustrate the threat, we can face a collision attack - the attacker may create two pieces of information (such as files) with the same one-way hash function value. It is worth noting that it is common to see advanced hackers using this technique to avoid detection and identification (Anti-Evasion Technique). The same logic applies for Preimage Attack, which may find the original input that allows the production of a one-way hash function value. That is, this attack may in some cases cause the leak of sensitive/confidential information. And, moving further, in the second Preimage Attack, an attacker may find the specific input that produces the same one-way hash function value of another input, which he already knows. That is, this attack is possible in some cases to cause sensitive/confidential information to leak.
Overall, from reviewing the threats and vulnerabilities, it’s crystal clear that the impact of quantum computing on encryption is paramount. However, the potential applications of quantum technologies are exciting and could revolutionize our lives, hence it’s unavoidable to grasp that as the age of quantum computing approaches, it is becoming increasingly clear that many of the encryption methods currently used by businesses, governments, and other organizations may become obsolete. This presents a significant challenge that requires urgent attention and action at both the national and international levels. To ensure the continued security and stability of our digital systems and economies, we must take steps now to address this issue and prepare for the advent of quantum computing.
According to experts, the threat posed by quantum computing could become a reality within the next decade. However, it is possible that this timeline could be shortened if certain nations are actively pursuing quantum computing technology in secret, seeking to gain a strategic advantage. The secrecy surrounding the development and realistic progress of quantum computing technology makes it difficult to predict exactly when it will become a threat, but the potential risks are significant and require immediate attention.
In conclusion, at Niagara Networks, we observe the industry progress and will adapt as part of our roadmap at a certain point in time with post-quantum cryptography compliance. Our strategic objective is to follow and implement future released NIST Quantum-Resistant Cryptographic Algorithms in our network visibility platforms.
However, the race to develop a secure "post-Quantum" cryptography scheme is ongoing, but last year it suffered a setback when two researchers were able to crack it on a laptop in just under an hour. This news came as a surprise to the post-quantum cryptography community, as the scheme was seen as a promising defense against the potential power of quantum computing. It is likely that there will be further developments and evolution in this field before the National Institute of Standards and Technology (NIST) gives its stamp of approval and releases the framework for wider use.
In the near future, Niagara Networks' visibility technology will be enhanced with post-quantum cryptography (PQC) and quantum key distribution (QKD) to ensure that encrypted communication is resistant to attacks from quantum computers once the relevant recommendations and ratification have been finalized. Stay tuned…
---
Niagara Networks are industry specialists in network visibility, providing advanced network solutions for the specific needs of individual enterprises and national large and complex networks.
Don’t leave your network vulnerable to security threats, schedule a consultation with one of our network visibility experts today to evaluate your network visibility challenges.

 By: Zeev Draer
By: Zeev Draer