Chief Information Security Officers (CISOs) are leading a battle against a moving target battle. Many attackers keenly innovate and can change tactics almost immediately. With the global cost of cybercrime reaching some $6 trillion annually by 2021, cybercriminals are motivated to hone and evolve their practices for big pay-offs.
But cyber attacks don’t have to be an inevitability. As you solidify your cybersecurity strategy for 2020, the following recommendations will put you on the path to defending against even the most advanced attacks over the long term.
Introduce Agility into Your Network Security
Most security organizations are exceedingly slow in being able to roll out new or update existing solutions deployed on their networks to identify attacker activities and thwart their efforts. New technologies are constantly being developed to stay ahead of attackers. Unfortunately, because of long, involved internal processes to get authorization to deploy something new or change something existing, most networks lag in their ability to deal with the latest attacker tactics.
Consider the Open Visibility Platform [link] to establish a “pre-approved” deployment hub for an unlimited number of solutions and give them the exact traffic they require, delivered in exactly the right way. Internal politics and processes, as well as limited rack space and ports, will no longer be a limitation
Bringing DevOps and SecOps Together
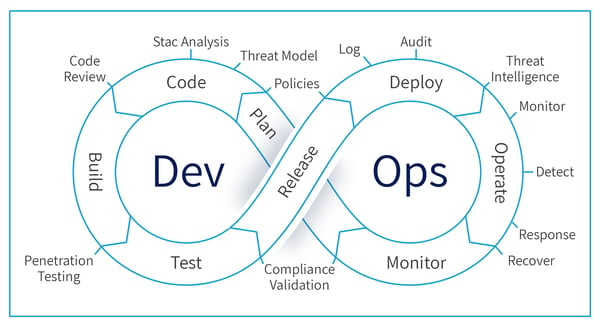
In recent years, security teams have just started getting involved with DevOps conversations and workflows. But as pressure increases to stay ahead of advanced attackers, more and more security leaders are considering DevSecOps practices. This year, bringing DevOps to SecOps will be a major factor in your success.
DevOps aims to decrease time to market, increase product quality, and improve software reliability by accelerating feedback loops for all involved. When security is left out of the conversation, those benefits will never come to fruition as you try to play catch-up on existing continuous integration and continuous deployment pipelines.
By integrating yourself (and your team) into larger DevOps conversations about culture, automation, measurement, and collaboration, you ensure that vulnerabilities don’t make their way into development processes.
Forging a Path to Automate Regular Chores
Efforts to automate regular administrative functions in security to enable more time for the most important matters can relieve short-staffed, overworked teams. At the same time, minimizing human error while scaling cybersecurity efforts to match increasingly sophisticated attackers have made automation a major CISO priority in 2020. Rather than focusing on tedious or mundane tasks, automation frees up resources for your team to focus more on engineering, root cause analysis, and further automation.
Common strategy is the adoption of Security, Orchestration, Automation and Response (SOAR) tools and Robotic Process Automation (RPA) solutions to address the need for more automation. While these tools play an important role in automating your operations, they are incomplete without a pervasive network visibility layer working as their foundation.
Focusing on network visibility first and foremost will ensure your automation efforts are fueled by 100% of network relevant data. With a pervasive visibility layer in place, you’ll know that malicious packets aren’t slipping through the cracks of your increasingly automated security architecture.
Leveraging Visibility Tools for Compliance
New regulations like GDPR and CCPA have brought compliance concerns to the forefront of CISO conversations. Now, even a minor data privacy issue can cost your company millions of dollars. And while addressing data protection has always been your responsibility, there’s never been more pressure to do so flawlessly.
However, the volume of data that comes in and out of your network on a daily basis makes it harder than ever to maintain data privacy. Security intelligence platforms can only analyze the data that’s available to them, which means network visibility has to be a priority for compliance.
When you have network visibility solutions that can intelligently route traffic, analyze data in real-time and mask specific privacy- defined fields in data, you’re able to clearly see and address potential compliance issues before they become problematic for the business. Knowing exactly what information is stored on your network, where it’s stored, and whether or not it’s protected comes down to your ability to maximize visibility.
Preparing for More Elusive Attacks
In recent years attackers have found that one of the most effective ways into a network is through gaining control of a user account or computer and then use its legitimate privileges to gain access to systems, networks, and storage. Some attackers may try brute-force password cracking, but phishing schemes, website-based exploits or human engineering are most productive. This means you have to expect that attackers will get into your network. The job becomes finding them as soon as possible..
Making Cybersecurity More Proactive
The biggest data breaches of all time have one thing in common—they grew exponentially as a result of reactive cybersecurity strategies. Attacks on companies like Target, Yahoo!, and Anthem operated behind the scenes for months (or even years) before anyone discovered the issues.
While security teams have gotten much better at identifying and resolving incidents quickly, many strategies still take a reactive approach. Becoming more proactive than ever in your cybersecurity operations is critical to success in 2020. While this may seem easier said than done, it’s important not to expect a single universal solution that will drive the transition. Rather, proactive cybersecurity is all about creating a baseline of activity for your network, implementing real-time monitoring and analysis tools, and configuring systems to shut down automatically in cases of anomalous behavior.
When you can address anomalies in network behavior rather than constantly putting out fires with full-blown security incidents, you’ll be able to protect your business assets more effectively.
Identifying Cloud Vulnerabilities
Concerns over cloud security have changed in recent years as the world’s largest SaaS, PaaS, and IaaS providers focused more heavily on preventing attacks and downtime. For some CISOs, guarantees from cloud providers about security have meant the in-house security team could avoid spending too much time addressing cloud vulnerabilities.
In reality, cloud vulnerabilities still pose a major threat—but from the provider’s side. Identifying cloud vulnerabilities is all about the way your network team configures cloud instances and automation processes. Applying API security controls to avoid attacks on management or applications APIs is highly critical and proves that CISOs haven’t dedicated enough resources to spotting these vulnerabilities.
Don’t let human error in cloud computing open the door for attackers to compromise your core network. Make sure your network monitoring and visibility tools extend to API security controls and cloud environments so you can stay on top of any potential issues before they get out of hand.
Every key to CISO success in 2020 revolves around one thing—your ability to maximize network traffic visibility for all tools, systems, processes, and employees. If that fundamental need isn’t met, you risk spending your entire cybersecurity budget on advanced tools only to find that attackers easily evaded them to attack your network.
In summary, you are only as secure as your weakest link and this is the year to create your pervasive network visibility layer. If you’re ready to do so, contact us today and find out how the Niagara Networks suite of solutions can help.

 By: Zeev Draer
By: Zeev Draer