Improving the Internet: A Call to Action
I took a seminar taught by a retired U.S. Army Command Sergeant Major with a PhD in Organizational Psychology. Talk to anyone who knows about the U.S. military and they will tell you that it is the Sergeants that actually run the Army and, before he retired, this guy had held the highest possible enlisted rank. His experience and managerial skills combined with his academic background made him uniquely qualified to deal with management issues across a broad spectrum of situations.
He had a simple, but sound approach to analyzing a problem, based on asking the following three questions:
• What happened?
• What did we learn?
• What are we going to do about it?
His three questions are in fact paraphrases of a common systems analysis methodology used to address problems in both human networks and computer networks. This methodology is often stated in three steps:
Observe. Decide. Act.
As discussed in an earlier post, improving the Internet by applying massive change is a long way off. Continuous incremental improvements, like watching ants in a colony continuously tunnel and evolve their domain, is a much more likely outcome.
This brings us to the topic at hand. The efficiency, effectiveness and security of the Internet can be dramatically improved by a comprehensive application of Network Monitoring and Visibility technologies.
For those of you that are using Network Monitoring and Visibility solutions from Niagara, or other vendors, the first component of a Network Monitoring and Visibility system is a comprehensive physical overlay network that taps into the data streams at key points and feeds monitoring and analysis tools. 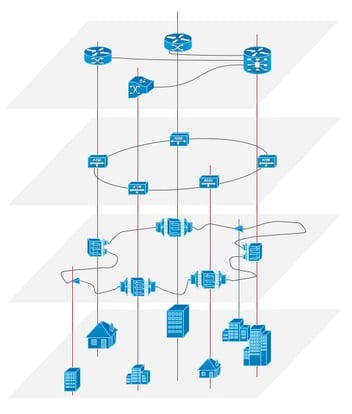
Today’s monitoring switches from Niagara and other vendors can deliver data to monitoring and analysis tools, in either raw or processed form, without disrupting the user experience or data flows to applications. The result can be a dramatic positive impact on the efficiency, reliability and availability of the Internet.
The same technology, when combined with Network Bypass devices, can be used in-band to create uber-multifunction security gateways. The days of simple firewalls are rapidly disappearing, even in smaller enterprises. The need to protect systems and users from today and tomorrow’s threats requires an array of capabilities that no single vendor can deliver. An in-band Monitoring and Visibility solution with intelligent Bypass is key to providing the capabilities required.
The data pipes are also too big for the tools. Network routers and switches are already available with 100Gb/s ports and 400Gb is looming ahead. With a Network Monitoring and Visibility solution, traffic can be screened, filtered, and load-shared across banks of lower speed devices that can perform various types of deep packet inspection (DPI) and data analysis. With threats increasing in sophistication, where analysis tools need to be frequently upgraded with the most up-to-date threat patterns, this approach allows upgrade of the hardware or software, without taking the networks down.
A comprehensive overlay approach to Network Monitoring and Visibility provides the highest level of protection. Separating three stages of Observe, Decide, and Act, where each stage is performed by discrete pieces of equipment, provides a much higher level of fault isolation, security, and upgradability. Furthermore, this overlay approach protects users and systems more than integrating the functions into network switches and security appliances ever will.
Instead of reinventing the Internet, we need to improve availability, user experience and security through Network Monitoring and Network Visibility.
There are industry experts that talk about a utopian future, where security threats are eliminated. Is this realistic? What can we learn from other complex systems?
Let’s start with humans. Most of us function pretty well, most of the time, all the while being host to a large array of potentially harmful bacteria and viruses. Through a complex set of defensive and offensive mechanisms, the human body keeps them from us carrying on our daily lives. Perfect? Absolutely not.
Researchers all over the planet are working on fighting cancers, extending longevity, and improving quality of life. But none of them are pursuing a strategy based on eliminating all threats. We need to accept and embrace the idea that a parallel path exists to the future of the Internet. One in which a continuously improving set of capabilities relentlessly progresses to deal with evolving threats that can be observed, analyzed, and acted upon.
Contact us. We will help you understand how
 By: Harry Quackenboss
By: Harry Quackenboss