Are We Already Numb to Cyber Attacks?
On Wednesday, December 14, 2016, Yahoo announced that 1 billion user accounts were hacked in 2013 by what they said was a “state-sponsored” attacker. If, like me, you presumed that this was merely an update on the breach that Yahoo announced back in September of this year, then I suggest you keep reading this post.
This attack was a separate incident from the one revealed in September. And I’m not sure this is a contest or if anyone is keeping score, but based on what was announced to the public, Yahoo is (ahem!) on top of the pile, if you will. So, what happens next? Despite the long list of hacks already disclosed, much of the IT world seems resigned to this being the new norm; however, I don’t see how this attitude can last much longer.
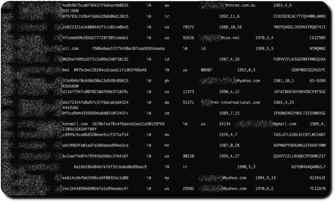
I hope what does happen next is if you are reading this post and have a Yahoo ID (with over a billion records hacked, there’s a pretty good chance that even if you do not you’re still vulnerable), that you head over to PwnedWebsites and follow the instructions to check if any of your accounts have possibly been breached. Be sure to enter every current or past online username and email address you can remember, including the Compuserve and AOL accounts, every company, school, and club email, your MySpace account (remember now?), Android forums, Cannabis.com… the list goes on and on.
Long-Term Impacts
 One can only speculate about the long-term impacts of this latest data-hacking revelation. This is BIG, really BIG. But it also fits into a pattern of increasingly frequent hacking efforts that are becoming even more substantial. And here we are still learning about these security breaches well after the fact; in this case, three years later. If you work in or around the information technology sector, you owe it to your community to ask this crucial question one more time—are we doing enough?
One can only speculate about the long-term impacts of this latest data-hacking revelation. This is BIG, really BIG. But it also fits into a pattern of increasingly frequent hacking efforts that are becoming even more substantial. And here we are still learning about these security breaches well after the fact; in this case, three years later. If you work in or around the information technology sector, you owe it to your community to ask this crucial question one more time—are we doing enough?It is now abundantly clear that the definition of what constitutes adequate protection against cyberattacks is changing. These attacks are becoming more numerous, more sophisticated, and harder to detect. This arms race of measures and counter-measures between the hackers and every organization responsible for user and enterprise data will continue to escalate.
Along with the changing definition of “adequate protection,” we are likely to see evolving standards in regard to what organizations and individuals are responsible for from a legal liability perspective.
Last year, a first-rate firewall was considered sufficient for most organizations. But looking to the future, more sophisticated, multi-faceted, parallel approaches will be required, including behavioral analysis, data inspection, data leak detection, artificial intelligence-based malware detection, and more.
To effectively address these needs, financial institutions, government agencies, contractors, service providers and the like, who already deploy security delivery networks using devices, such as Niagara Networks’ portfolio of Network TAPs, Network Bypass Solutions, and Network Packet Brokers, will need to expand their Network Visibility infrastructure. Meanwhile, organizations that have yet to implement network security and Network Visibility fabrics will be forced to quickly move in that direction.
.png)
 By: Harry Quackenboss
By: Harry Quackenboss