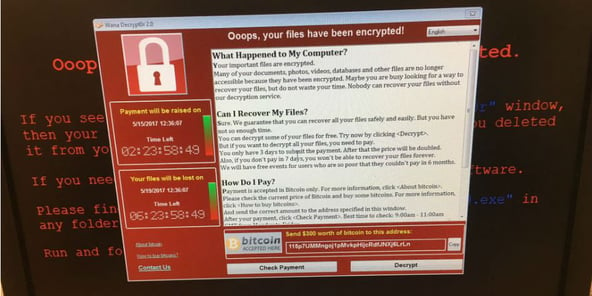
Organizations across the world are still continuing to come to terms with last week’s massive “WannaCry” ransomware attack, which crippled IT infrastructure on an unprecedented scale. In this post, we examine the nature and impact of this threat and why it requires pervasive and advanced network visibility for dynamic threat detection and remediation.The recent attack that cyber security experts judge to be one of the fastest spreading and potentially damaging cyber attacks to date is based on a modified version of the WannaCry ransomware virus first used by criminal networks online, earlier this year. Ransomware encrypts data on computers and demands a fee typically payable in untraceable digital currency to unlock them.
The malware has the capability to scan heavily over TCP port 445 (Server Message Block/SMB), spreading similarly to a worm, compromising hosts, encrypting files stored on them, and then demanding a ransom payment in the form of Bitcoin. Importantly, the malware not only scans internal ranges to identify where to spread, it is also capable of spreading based on vulnerabilities it finds in other externally facing hosts across the internet.
Security officials in the UK, which has been one of the most affected countries, currently believe that the attacks are the work of a criminal group, though they are still working to assess the full nature of the attack. In the UK, more than a third of the 260 hospital trusts across the country have been hit.
The WannaCry outbreak has hit computer networks in at least 11 other nations beside the UK, including US, France, Spain, Russia, and China. As the attack spread, FedEx, the US delivery services company, said it was “experiencing interference with some of our Windows-based systems caused by malware.” The Russian interior ministry confirmed that 1,000 of its computers had been affected, about 0.1 per cent of the total, but said its servers were not harmed.
China was also hit hard by the attack, with over 29,000 organizations falling victim to the ransomware. Chinese government bodies for transport, industry, social security and immigration are among those which became infected with WannaCry, while schools colleges and an energy firm have been hit, per news reports.
The cyber attack halted or reduced the output of at least five sites of the French automaker Renault. Besides a plant in Douai in northern France, other sites attacked included a van plant in Sandouville, a small car plant in Slovenia, the no-frills Dacia plant in Romania, and a factory shared with Nissan in Chennai, India.
So, what does this mean?
It means pervasive cyber warfare, capable of doing damage in so many ways, underscores the need for proactive threat detection and remediation built upon a foundation of advanced network visibility. Since attackers can quickly utilize every network segment for spreading malware, effective visibility means continuous access to the vast amounts of traffic flows and metadata across every corner of the network.
Niagara Networks delivers just that. It starts with Niagara’s network packet brokers with the ability to aggregate traffic flows via a family of high-density taps and nodes that can then deliver copies of that traffic to network security devices.

 By: Niagara Networks
By: Niagara Networks