In the spirit of Halloween, people are watching horror movies, trick or treating, dressing up in scary costumes, and it may not be easy to tell who someone is or supposed to be. The same thing goes for Networks - sometimes you don’t know if you’re being attacked or what ghosts may be creeping up on you. Network Engineers and IT Security Professionals are constantly trying to hunt down those ghosts and prevent a disaster from occurring in their networks.
So, we wanted to help you prevent some of those nightmares by sharing with you some monsters that may be lurking in the shadows of your Network.
Intruder on your network:
Have you ever felt like someone is following you? Better hope it’s not someone like Michael Myers or a security breach/hack. These hacks are very common nowadays. If you are not monitoring your network in real time, you might miss something that could prevent these intruders from entering your network. Be sure to use network visibility and network security tools in conjunction so that you can prevent this nightmare from occurring!
Haunted by Ghostface – Lack of Troubleshooting
Just like Ghostface, Network Engineers may not know the cuase of their problems. They come across troubleshooting VoIP, storage, virtual desktops and other IP-based applications on a daily basis. The more traffic in a network, the harder it is to diagnose the correct problem. Use a Multi-purpose visibility platform to increase your Network Visibility and help you solve these troubleshooting nightmares.

Network Zombies
Network zombies slow down the network and cause network downtime. Reliable network connectivity is extremely critical. Many companies such as healthcare, retail, high-speed trading and banking establishments cannot tolerate even a few minutes of network downtime without having a possible negative effect on their business. Preservering network connectivity is especially critical in inline monitoring deployments. Network Bypass Technology ensures zero downtime so you won’t need to worry about any zombies this Halloween!Dracula sucking the access out of your network
Another nightmare that you could encounter is trouble accessing your wireless network or virtual environment. Don’t let Dracula suck the access of your network and hinder network performance through satellite radio and streaming video. Be sure to use active vampire-hunting tools to keep your network performance and access available.
No Visibility to Monitoring and Security Tools
 A common horror that Network Engineers and IT Security Professionals come across is not having any visibility on what gets passed on to their security and monitoring tools including Intrusion Prevention Systems (IPS), Data Loss Prevention (DLP), content delivery, WAN optimization, Deep Packet Inspection (DPI) systems, and Unified Threat Management (UTM) appliances.
A common horror that Network Engineers and IT Security Professionals come across is not having any visibility on what gets passed on to their security and monitoring tools including Intrusion Prevention Systems (IPS), Data Loss Prevention (DLP), content delivery, WAN optimization, Deep Packet Inspection (DPI) systems, and Unified Threat Management (UTM) appliances.
People often tend to neglect the monitoring infrastructure and the importance of these appliances and tools, and allow these tools to operate without any specific intelligence. The management and optimization of these security and monitoring tools are instrumental for well-functioning, secured networks. Niagara's visibility solutions provide the intelligence required for improving performance, monitoring and security of networks, thus enabling trimming, optimizaiton,a nd manipulation of any packet sent from production network to Niagara Networks' disributed architecture. NOSE provides end-to-end visibility for Network Security teams.
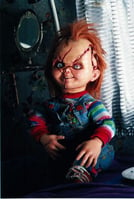
Hidden Blindspots
Although these blindspots may be small, if you learned anything from Chucky, it’s that you can’t underestimate the power of something small. The blindspots in your network could be infected packets that can cause various security attacks and problems to your network. Be sure to identify these unknown packets with Network TAPs or Network Packet Brokers, before it's too late!
Most importantly, don't be too frightened away because we are here to help! Contact us today and we will help you avoid these nightmares.
Happy Halloween!

 By: Niagara Networks
By: Niagara Networks