How to Achieve Hybrid Network Visibility with a Central Controller
In the first part of this mini blog series, we talked about the new reality for IT leaders—hybrid networks.
Despite the all-or-nothing excitement in the early days of cloud computing, it’s clear that on-premises infrastructure isn’t going anywhere anytime soon. Rather, the key to network success is finding your perfect balance of on-premises, public cloud, and private cloud infrastructure.
If you want to succeed with your hybrid network, you need to plan for visibility. Achieving pervasive hybrid network visibility may seem challenging, but it’s far from impossible.
The Basics of Pervasive Network Visibility Remain
52% of IT leaders say lack of hybrid network visibility leads to troubleshooting problems. You can avoid falling victim to this by correctly instrumenting your network to provide you with total network visibility.
Whether you’re architecting a traditional network or a hybrid network, your focus should still be deploying a comprehensive network of performance management, monitoring, and security appliances.
With those solutions in place, you have to implement the right support system to ensure each tool receives all packets necessary to keep your network running smoothly. That’s where the three keys to pervasive network visibility come in:
- Network Taps: Copy your traffic and mirror ports at critical points of the network so you can gather data, monitor for performance, or feed an intrusion detection device.
- Network Packet Brokers: Analyze traffic to deduplicate and load balance across multiple visibility tools.
- Bypass Switches: Eliminate points of failure across the network by ensuring network links stay online even if an active, inline appliance fails.
With a well-designed layer of taps, packet brokers, and bypass switches, you can quickly deploy new appliances and adapt to evolving network needs without sacrificing visibility.
However, the added complexity of a hybrid network requires you to do more than just deploy the traditional support components. You need:
- Instrument your cloud with virtual equivalents of the traditional Network Taps and monitoring tools that give you visibility on the cloud performance.
- Centralized control over the visibility layer can help you overcome hybrid network challenges.
- Application Centric management strategies that take into consideration the performance of assets in different network segments and how they interact with each other.
Hybrid Cloud Specific Challenges and Strategies
A Hybrid Cloud introduces Network Segmentation. While this reduces your attack surface, increases access control and streamlines compliance, it creates challenges for your Network Visibility. Assets on public clouds require special instrumentation to increase visibility and better management strategies to be able to maintain a comprehensive view of your network. The segmentation also requires that you establish a management and monitoring infrastructure capable of combining the application performance and traffic analysis on each of your segmented networks.
To increase your Public and Private cloud visibility you should add the following tools to your Network Visibility strategy:
- Virtual Network Taps - that sit next to the virtual network switches at your public and private clouds, allowing you to capture and forward traffic to be further analyzed for both security and performance reasons.
- Hypervisor Agents or Virtual Information Controllers - that sit right on your private cloud hypervisors, collecting information about your infrastructure performance for both your hosts and your virtual systems.
- Application Centric Monitoring - that analyzes the traffic, its flow across its components (regardless of their location), and how each network component impacts the quality of the end user experience. With it, you gain the ability to correlate virtual infrastructure to application performance and pinpoint problems root causes.
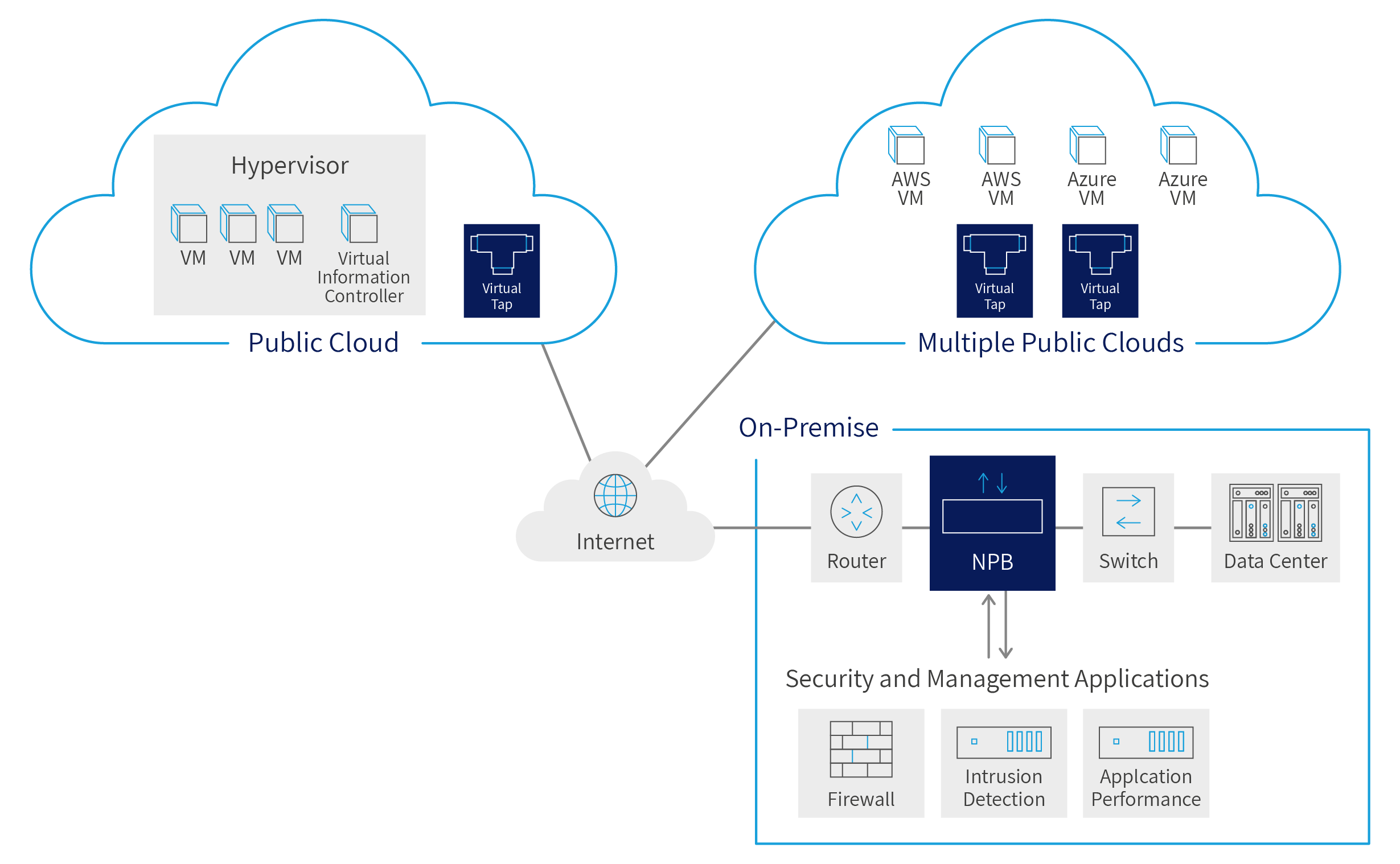
Fig 1 - Hybrid Cloud Monitoring Points
In the diagram above we extend our traditional Network Visibility strategy to consider the following types of Clouds:
-
Multiple Public Clouds - where the application owner rents compute power to run our applications on the providers that offer the best product for the particular application needs. The same application may be using resources from multiple providers - Amazon, Microsoft, Google, etc. We want to tap on each of the virtual networks supporting the application, combining the power of multiple measuring points into a total visibility situation.
-
Private Clouds - where we have control and responsibility for the management of the cloud infrastructure, and we also have the interest and ability to create virtual networks specialized for our applications. These may be built by the organization that owns the application or may be built by a provider of cloud services - but in either case, there is greater ability to instrument the infrastructure. While we still have the ability to tap, we also have the ability to instrument at the Hypervisor level.
The Value of a Hybrid Network Visibility Controller
Before hybrid networks became the norm, we called centralized visibility control management a force multiplier for the links you cover. Now that hybrid networks have become the norm, central visibility control management is more of a necessity than a luxury.
With centralized control, you manage all independent visibility appliances as a single virtual switch fabric. That means that even though you have various visibility solutions deployed for on-premises, public cloud, and private cloud aspects of the network, you can break down silos and manage all of your network segments together. As a result, you maximize the flexibility and efficiency of your network visibility solutions rather than succumbing to the East-West challenges of hybrid networks.
This is what sets the Niagara Networks approach to pervasive hybrid network visibility apart from the crowd.
Our own Niagara Visibility Controller (NVC) is a unified manager that provides an overview of all packet brokers, taps, and bypass switches across your network while also providing central access to configuration details. Managing hybrid network as a single fabric eliminates concerns that disparate aspects of your architecture will negatively impact visibility.
With NVC you can understand what traffic is being managed by what appliance, identify gaps in coverage, and ensure redundancy and availability. You can visualize the efficiency of your security and monitoring applications and identify better ways to make the best use of the resources you have. You also optimize your resources and reduce your costs by identifying opportunities to de-duplicate traffic and re-use existing management tools.
You can’t manage what you can’t see. And in recent years, that’s been a serious problem for IT leaders migrating workloads off premises. But when you have a central solution like the NVC providing real-time insights into network performance and security, you’ll never lose sight of hybrid network traffic.
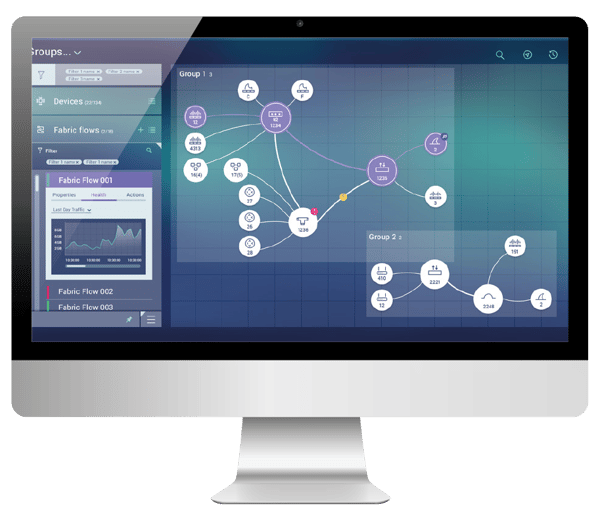
Fig 2 - Niagara Visibility Controller
If you want to learn more about simplifying your hybrid network to maximize visibility, contact us today for all the details about our Niagara Visibility Controller and our Public and Private Cloud management tools.
![[PART 2] Network Visibility and Hybrid Networks | Niagara Networks](https://blog.niagaranetworks.com/hubfs/blog%20(29).png)
 By: André Vink
By: André Vink