As a network security specialist, there’s no doubt that one of the network security tools you make use of is SSL (Secure Sockets Layer). However, SSL isn’t only used by security specialists to protect highly confidential data.
Whether most people realize it or not, a growing number of websites are adopting HTTPS, even if they don’t handle confidential data. HTTPS is an SSL implementation that’s used to protect the data between your browser and a server. The Let’s Encrypt open certificate authority reported that, as of January 2017, over 50% of Firefox web traffic was loaded through HTTPS. NSS Labs expects this number to increase to 75% across all browsers by 2019.
However, this increasing popularity for SSL hasn’t come without a cost, and a number of challenges have arisen. Without SSL interception (or decryption), encrypted traffic is invisible to enterprise security measures and increases the enterprise security risk. Encrypted SSL links are mediums through which data leaks can occur or through which malware can penetrate and infect the organization and its users.
While SSL interception is important in securing the enterprise, it’s vital that you choose the right type of deployment and that you implement it correctly, as SSL interception may introduce unintended end-to-end vulnerabilities.
There are two main types of deployments for SSL interception: Passive and active. Here is a breakdown of these two types of SSL deployments, their advantages, and the challenges they present to network administrators who want to ensure network visibility and establish a solid network firewall.
Passive SSL Deployments
Passive SSL deployment of the SSL Appliance is done with one goal in mind: Gather traffic for analysis and reporting purposes. However, this type of SSL deployment doesn’t affect the traffic itself, since no immediate action needs to be taken. This could be compared to financial auditors who check your financial reports to see if there are any errors or unusual activity. They aren’t there all the time, checking every financial transaction you make, but will check your records after the transaction has been completed. The same idea applies to Passive SSL decryption.
The benefits of passive SSL deployment include less risk with implementation itself, far fewer vulnerabilities, higher performance, and ease of implementation. However, due to the fact that you aren’t immediately checking your traffic, your ability to react in real-time and block any malicious data is limited. The same concept applies to Passive SSL decryption.
There are two types of passive SSL visibility implementations:
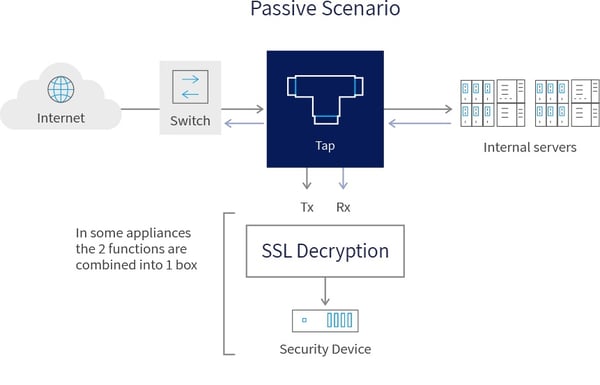
- Passive-Tap — This type of implementation can only be used with the certain ciphers and encryption methods, specifically in regard to inbound SSL inspection. In this implementation, a tap device is used to copy the traffic, after which the copy is forwarded to the out-of-band SSL Visibility Appliance for decryption. Once decryption has been completed, the decrypted traffic is then passed on to the attached security device for analysis and reporting. The original traffic continues along the network as normal.
- Passive-Inline — In this implementation, the SSL Visibility Appliance is included inline, which allows it to decrypt and then re-encrypt the traffic so that it can be passed onto the next device in the network. A copy of the decrypted traffic is forwarded to the security device for analysis and reporting. Because the SSL Visibility Appliance is inline encrypting and decrypting the traffic, this implementation has more in common with the Active SSL deployments described in the next section.
Active SSL Deployments
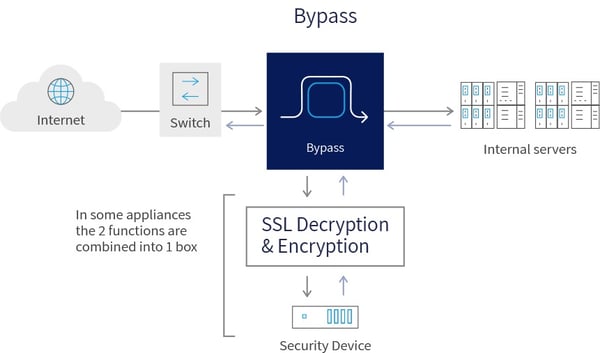
Active SSL deployments are referred to as Man in the Middle (MITM) implementations because they act as a middleman in SSL network communication. In this type of implementation, your SSL Visibility Appliance and active security device are connected inline, which means they are a core part of your network and traffic must pass through them before moving onto the next device. It is this type of SSL implementation that is particularly vulnerable to implementation issues.
Here’s a quick breakdown of how network traffic works in this implementation. The role of the SSL Visibility Appliance is to decrypt the traffic and then pass it along to the active (inline) security device. The security device will check the traffic to see if it is secure or if it contains a malicious payload, such as a virus or malware. If the traffic is determined to be malicious, it will be blocked by the security device and the SSL Visibility Appliance will drop the flow of traffic. Traffic that is secure will be forwarded back to the SSL Visibility Appliance, re-encrypted, and passed on to the next device in the network. The major benefit this offers is that it allows you to protect your network in real time. Malicious traffic is blocked and prevented from having a negative impact on your network and devices.
Think of SSL Decryption like package inspectors at a post office. They perform random checks on packages by opening them and making sure the contents of the package meet post office regulations. If they are, they reseal the package and send it on to its intended address. If the contents do not meet post office regulations, the package is quarantined. An SSL performs a similar function for network traffic, but for every “package” that comes in.
As you can imagine, checking every package at the post office would drastically slow down the rate that packages were delivered. Active SSL deployment may reduce the performance of your network for this exact reason. Where your total SSL traffic throughput is higher than that of the SSL Interception. In order to address this potential performance issue the SSL Visibility Appliance typically has filtering capabilities that enable you to select which SSL traffic to inspect and which to cut through without the decryption and re-encryption cycle.
In cases where you must inspect all traffic, you need to decide what to do with the excess data. Blocking it might mean you are preventing important data from reaching its destination, while allowing it to continue on the network might mean you're allowing malicious traffic in.
It’s vital that you implement your active SSL solution correctly, and failure to do so could leave you vulnerable to attacks in the most unexpected ways. This study highlights how poor SSL Interception implementation impacted connection security. The study investigated popular antivirus and corporate proxies, finding that many reduced connection security and that others introduced vulnerabilities.
Implementing the Right SSL Deployment for your Organization
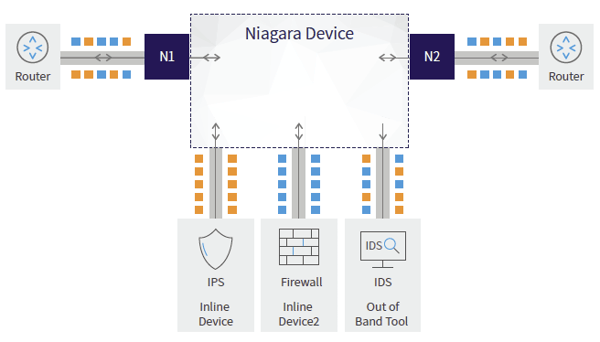
Implementing SSL Interception is a complicated process and network security specialists should take steps to ensure they choose the right implementation for their needs. One of the factors that help network professionals overcome some of the challenges associated with SSL Interception, is the use of Network Packet Brokers (NPBs).
NPBs give you flexibility in deploying inline or out-of-band solutions and to choose which part of your traffic needs to be sent to the SSL solution, and this way, relieve some of the performance issues associated with capacity of the tools. This is done by Other higher end Network Packet Brokers offer integrated SSL Interception off-loading.
To find out more about how packet brokers can optimize your SSL implementation, schedule a consultation with a Niagara network visibility expert.

 By: Yigal Amram
By: Yigal Amram